April Fools' Day passes swiftly, taking with it the jokes and hoaxes that make us question reality for a moment. However, scammers remain relentless, ignoring the calendar.
Spring marks a peak season for cybercriminals. It's not due to negligence, but because our busy schedules and divided attention make us vulnerable to subtle threats sneaking through unnoticed.
Below are three current scams targeting not just the naive, but alert and diligent employees navigating their daily tasks.
As you review these scenarios, ask yourself: Does my team consistently pause to identify these threats before it's too late?
Scam #1: Deceptive Toll and Parking Fee Texts
An employee receives a text message alerting them of:
"An outstanding toll charge of $6.99 is due. Pay within 12 hours to avoid penalties."
The message cites authentic toll systems—E-ZPass, SunPass, FasTrak—tailored to the recipient's location. The modest fee and busy timing make it easy to overlook caution.
They click the link and pay, unaware it's a phishing attempt.
In 2024, the FBI logged over 60,000 reports of fraudulent toll texts, and incidents surged 900% in 2025. Cybercriminals have created over 60,000 bogus websites mimicking legitimate toll platforms, signaling just how lucrative this fraud has become. Shockingly, some victims reside in states without toll roads.
This scam's success lies in its plausibility: small fees and common toll experiences lull recipients into compliance.
The best protection? Real toll agencies never request immediate payment via text links. Train your team to verify any such claims directly through official apps or websites and to avoid replying to these messages, since any response confirms active contact for further scams.
Prioritizing verified processes over convenience shields your business.
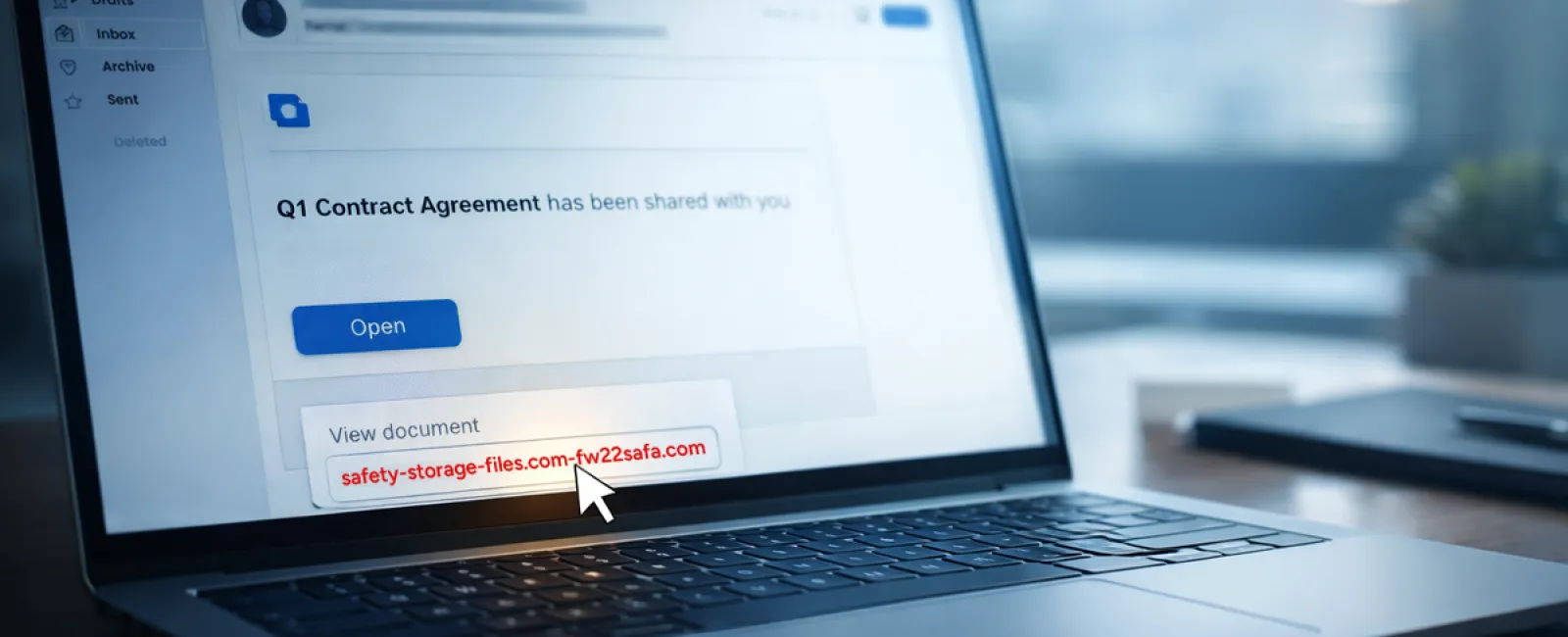
Scam #2: Fake File Sharing Alerts
This scam seamlessly integrates into daily workflows.
Employees receive emails indicating a document has been shared—often a contract via DocuSign, a spreadsheet through OneDrive, or a file in Google Drive.
The sender appears legitimate; the formatting matches genuine notifications.
Upon clicking, employees are prompted to log in and inadvertently provide their credentials, granting attackers access to your company's cloud systems.
Attacks exploiting trusted platforms rose 67% in 2025, with Google Slides phishing links alone increasing by over 200% within six months. Alarmingly, employees are seven times more likely to click links from known services versus random emails.
More sophisticated schemes involve compromised accounts sending file-sharing notifications that bypass spam filters, as these emails originate from official servers.
Effective defenses include: instructing staff to access shared files only by logging directly into platforms, limiting external sharing permissions, and enabling alerts for unusual logins—changes your IT team can implement swiftly.
Simple habits yield powerful protection.
Scam #3: Highly Convincing Phishing Emails
Gone are the days when phishing emails were easy to spot due to poor grammar and sloppy craft.
In 2025, AI-generated phishing emails achieved a 54% click rate—more than four times higher than human-crafted attempts. These messages reference real companies, job titles, and workflows, scraped from public sources, making them incredibly convincing.
Attackers now target specific departments: HR and payroll receive false employee verification requests, finance teams encounter vendor payment change requests, with some tests showing 72% engagement on vendor impersonation attacks—90% more than other phishing types.
Guardrails include: verifying any requests involving credentials, payment details, or sensitive information through a separate channel such as a call or direct message. Encourage hovering over email addresses to confirm the sender, and treat urgent tones in emails as red flags.
Genuine security never pressures users into quick decisions.
What It Ultimately Means
Each scam exploits trust, authority, timing, and the rush to act swiftly.
Therefore, the real vulnerability is not a careless employee, but expecting every person to consistently slow down, verify, and make flawless judgments under pressure.
If a single hasty click can disrupt your operations, this points to a systemic process issue—not a personnel fault.
Fortunately, process problems can be addressed effectively.
How We Support You
Most business owners prefer not to add more tasks or become the sole guardians against cyber threats.
They want assurance that their company remains protected quietly and efficiently.
If you'd like to assess your team's current risk exposure—or you know another leader who should—let's connect.
Book a no-pressure strategy session to discuss:
- The threat landscape specific to businesses like yours
- How cyber risks often infiltrate everyday tasks
- Actionable steps to reduce risk without hindering productivity
Schedule a complimentary consultation to explore your options with confidence—no gimmicks, just clear conversation.
Click here or give us a call at 978-664-1680 to schedule your free 15-Minute Discovery Call.
If this message isn't relevant to you, please share it with someone who'd benefit. Understanding these threats can transform a "would've clicked" into a "blocked attempt."